Accelerate Incident Response with Next-generation Network Access Visualization

“If you really want to protect your network, you really have to know your network”
The advice stated by Rob Joyce (former Chief of Tailored Access Operation at the NSA) in his presentation during the USENIX Enigma conference is gaining further importance in light of the recent SolarWinds attack. For incident response teams who had to investigate the breach inside their environment, a lack of detailed knowledge on networks and connected assets turned their investigation into month-long efforts filled with frustration. The issue of network visibility and clear understanding of network access is affecting most organizations. Two of the top three service engagement findings published in the Dragos 2020 ICS Cybersecurity Year in Review last week are:
- 90% of service engagements included a finding around lack of visibility across OT networks
- 88% of service engagements included a finding about improper network segmentation
The core challenge behind these findings comes from the growing complexity of network configurations. A typical firewall configuration includes thousands of statements defining interface settings, access-control lists, and object groups among other categories. Similar to a programming language, network device configuration have bugs that can lead to unexpected consequences, such as enforcing network segmentation partially instead of fully.
Read-only Network Visualization Solutions to the Rescue
The speed at which incident response teams can answer key questions during an attack is crucial to prevent a catastrophic failure. For instance, they may need to understand which port and services are accessible when accessing the control network from a jump host connected to the corporate network. In addition, they need to be able to answer this type of question without relying on network management toolset that can write into the network, since they may be part of the issue (case in point: the SolarWinds Orion application). For these reasons, incident response teams need to be equipped with their own highly-usable solutions that can run outside of the network fabric. This means either offline or through an indirect and readonly connection.
This is an approach that we know well since we spent the last few years training network engineers and cybersecurity analysts to leverage NP-View and NP-Live in order to gain a clear understanding of their networks. The workflow consists in rapidly building a topology map from network device configuration files that serves as a foundation to communicate efficiently among different teams. The map needs to be extremely easy to navigate and understand by both technical and non-technical users. Similar to a heads-up display (HUD) in an aircraft, complex network constructs need to be presented with the correct level of abstraction in order to convey enough details without being overwhelming. A key feature to achieve this objective is to be able to generate a stepping-stone access map.
Breakthrough Insights with Stepping-stone Access Maps
A stepping-stone access map combines end-to-end connections inferred with a path analysis into multi-hop connections. Each hop, or stepping stone, could be used by an attacker to move laterally. For example, a vulnerable web server that is accessible in a DMZ could be exploited and used as a stepping stone to penetrate further into a protected network. In the example below, a vulnerable data historian was selected at the bottom of the map (highlighted with dark circles) and NP-Live analyzed access rules and routes in all the firewalls (red-brick icons) in order to highlight:
- Nodes that can be directly accessed from the data historian (in red)
- Nodes that can be indirectly accessed from the data historian (in orange)
An indirect access means that coming from the data historian, an attacker would have to compromise a red node before being able to access an orange node. This type of visualization provides important insights to understand how defense-in-depth is implemented and whether access policy gaps exist. Moreover, it helps everyone to understand critical asset exposure without having to become a firewall or a network expert. For incident response teams, this means precious minutes saved getting to the information they need to take action and also explaining the situation to their colleagues and their leadership.
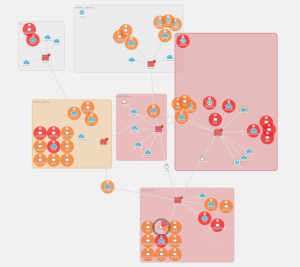
Stepping-stone access map generated by NP-Live to visualize which nodes are directly and indirectly accessible from a vulnerable host
