The Importance of Verification in Cybersecurity
Part 2 in a Blog Series on 3 Key Elements of a Cyber Resiliency Framework: (1) Verification, (2) Visibility, and (3) Velocity
The concept of verification is the process of checking and attaining information about the ability of an individual, a company, or an organization to comply with the standards. In the case of cybersecurity, verification is intertwined with compliance of regulatory standards based on industry best practices. The European Union’s General Data Protection Regulation (GDPR) is a good example of the linkage of verification and compliance, as are other regulatory initiatives in government such as CMMC and HIPAA.
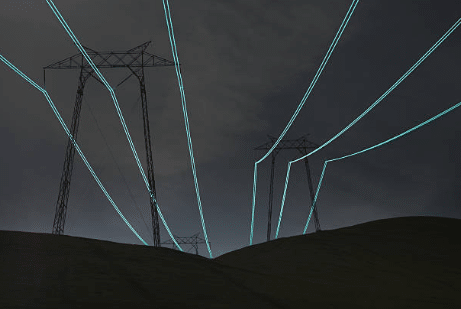
The energy and utilities industry requires a strong adherence to verification and compliance in its security posture. Recently, the Federal Energy Regulatory Commission (FERC) released its recommendations to help users, owners, and operators of the bulk-power system (BPS) improve their compliance with the mandatory CIP reliability standards and their overall cybersecurity posture. Staff from FERC’s Office of Electric Reliability and Office of Enforcement conducted the audits in collaboration with staff from the North American Electric Reliability Corporation (NERC) and its regional entities.
In its 2021 Staff Report ‘Lessons Learned from Commission-Led CIP Reliability Audits,’ the agency advised “enhancing policies and procedures to include evaluation of cyber asset misuse and degradation during asset categorization, properly document and implement policies, procedures and controls for low-impact transient cyber assets, and enhance recovery and testing plans to include a sample of any offsite backup images in the representative sample of data used to test the restoration of bulk-electric system cyber systems.”
The report also proposed improving vulnerability assessments to include credential-based scans of cyber assets and boosting internal compliance and controls programs to include control documentation processes and associated procedures pertaining to compliance with the CIP reliability standards. FERC report recommends compliance with CIP reliability standards – Industrial Cyber
Utility security can be viewed as the integration of national security into the power and electricity sectors, especially to protect the power grid. The North American Electric Reliability Corporation (NERC) is the regulatory authority with responsibility for the reliability of service to more than 334 million people. NERC’s standards are directly aimed at encouraging or mandating steps for utilities in protecting their operation.
NERC’s authority has led to critical infrastructure protection (CIP) standards that guide utilities’ planning and activities to eliminate or mitigate the many internal and external threat profiles. The CIP standards have evolved over time both in the scope of their focus and in the level of their authority. Utility Security: Understanding NERC CIP 014 Requirements and Their Impact (electricenergyonline.com)
VERIFICATION: Establishing a Baseline and Validating Risk Assessment Frameworks
Building effective verification begins by defining the scope of the verification process. You start by selecting those mission-critical assets — determine where they are, how critical they are to daily operations and who or what has access to them. To help initiate a strategy for verification within a physical and cyber resiliency framework for mission-essential systems such as utilities, it is helpful to understand the role of verification and compliance.
According to Marcus Sachs, Research Director for Auburn University’s McCrary Institute for Cyber and Critical Infrastructure Security, and former Senior Vice President and Chief Security Officer at the North American Electric Reliability Corporation, “compliance is, as everybody understands, the initial baseline. You’re required by law to be compliant with some framework. And NERC CIP is what we use for the bulk power system. I think most qualified engineers, and security professionals, know that is the baseline, the minimum that you meet.”
“NERC CIP is essentially the minimum security required as a Registered Entity under NERC,” agrees Patrick C. Miller, CEO at Ampere Industrial Security and Founder and President Emeritus of the Energy Sector Consortium. Like many cybersecurity experts, he believes that verification should be possible by any qualified party. Most organizations have SMEs within each business unit who handle the day-to-day operational aspect of compliance, but when it comes to guiding and validating evidence, that is usually performed by a central and authoritative compliance function.
According to Tom Alrich, Co-leader, Energy Sector SBOM Proof of Concept at National Technology & Information Administration US Department of Commerce, the biggest threats in the world are supply chain related, and SolarWinds and Kaseya demonstrated that not enough attention has been paid to those risks.
George Platsis, Senior Lead Technologist, Proactive Incident Response & Crisis Management at Booz Allen Hamilton states that “independent verification is your reality check. Even the best professional athletes have coaches. As good as you can be, you may have a blind spot, or something needs tweaking.”
Clearly, with the newly released FERC/NERC Staff Report on compliance and CIP reliability standards, it signals that verification will remain a key element of future policy. As our SMEs have noted in our discussion, the vulnerabilities and sophistication of potential security threats continue against CIP continue to expand. Therefore, it is important to incorporate a strategy that not only complies with best practices and standards, but also anticipates mitigating new risks. In our next blog we will discuss how visibility is essential to the risk matrix.
